8 common problems to avoid when performing network assessments
Dental practices can avoid catastrophic data loss, HIPAA violations by a network failure or breach by taking the proper precautions.
Over many of my past articles, I’ve written about the need for dental offices to conduct regular network assessments. In the close to 20 years that I’ve been doing this, I’ve seen practices go through catastrophic data loss and HIPAA violations by a network failure or breach that should never have happened.
I’m sure many of you may think, well, it could never happen to me. That’s pretty much the same attitude I had until I started seeing it happen to my clients. Here are the eight most common problems I see when doing network assessments:
- Inactive users: The only people who should have access to the network are current users of that network. When we show the user list to our clients after a scan, they often see names of people who haven’t been employed by the practice for years-or, more worrying, names they simply don’t recognize!
- Computers that have not logged in: A common situation in every office is computers are replaced by newer computers and the old ones given to staff, charities, etc. However, if you don’t remove those computer names from the domain, they can, in theory, still access the network over the internet.
- Misalignment of IT asset organization: Our scans reveal how the Active Directory is organized and lists all the security groups, computers, and users. When we compare the network configurations against the practice’s security policies, there are often discrepancies that need attention.
- Single point of failure: You probably don’t need a network scan to realize this, but there’s value in a report that shows that if your server fails, you’re dead in the water. This is why I’ve been preaching for years for offices to have a great backup and disaster recovery plan in place, as having two domain controllers and two servers for a small dental practice doesn’t really make sense financially.
- Inappropriate user access: Most of you would be surprised to know that for many networks we evaluate, every single user has full system administrator access; many of the practice management software companies are involved in this, as they recommend everyone have full access, meaning even a first-day employee has the same rights and privileges as the doctor. Obviously, this is NOT a good idea, even if the fact remains most users wouldn’t even know what level of access they have or how to exploit that-but some do!
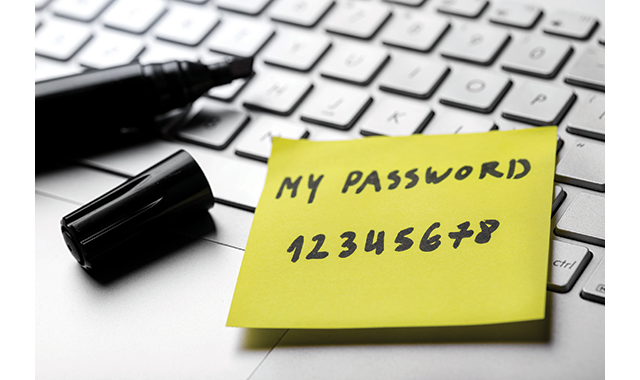
- Weak passwords: When we do a scan, we almost always find the practice doesn’t have good password policies in place. At a minimum, the password should have a certain complexity (eight or more characters and at least one number and capital letter), you should require the passwords to be changed on a regular basis, you shouldn’t be able to re-use older passwords, and the systems should lock out anyone who repeatedly tries to enter an incorrect password.
- External vulnerabilities: One of the most common vulnerabilities we find are open ports on the router or firewall. In some cases, clients know about this and are willing to take the risk as it’s required for how they work. But, in many cases, offices have no idea about these ports.
- Lagging patch management: The entire reason that most offices replaced their Server 2008 and Windows 7 machines was the lack of patches available after January 14, 2020. By all definitions, this is a HIPAA violation, and should be addressed.
Pretty much all the issues I discussed above can easily be discovered during a risk assessment-you know, the one HIPAA requires by law. I urge all offices to re-evaluate their risk assessment and make sure their networks are safe and secure.
